Join this three-day summit to hear cloud security and identity management experts, CISOs and security leaders share insights on the challenges common in both technology areas and the winning strategies available to address them.
Register for free thought leadership from the world’s top speakers, vendors and evangelists in the form of live webinars, panel discussions, keynote presentations, and webcam videos.
ESG Keynote:
Securing the Identity Perimeter with Defense in Depth
The core tenet of a zero trust strategy is least-privilege access. Yet, organizations continue to rely on user and machine identities that are susceptible to compromise, abuse and misuse, and theft. Risk is compounded by over-permissive, static access rights that provide little to no visibility into who and what is using access…
Learn how to safely manage identities and user access across multiple cloud environments.
Gain effective strategies to keep track of all your IT and data assets as well as what’s needed to assess risk and maintain compliance.
Discover best practices, technology and other helpful guidelines to protect your organization’s cloud environment.
Featured Panel Discussion:
Identity Management Is Essential to Cloud Security
Digital transformation and the evolution of identity in the workplace — spurred by decentralization, cloud adoption and remote work — have exposed the fact that old methods of identity and access management have outgrown traditional security protections, posing major risks. Adaptable and agile security architectures with a spotlight on identity are a…
A Special thank you to our Sponsors!
Diamond

Platinum

Gold

In Partnership


Audience
CISOs, CIOs, CTOs, MDs, Heads, EVPs, SVPs, VPs, Directors, Managers, Advisors, Partners and Consultants within:
IT / IT Security / IT Operations
Network Security / Systems Engineering
Internal Audit / Compliance / IT Risk
Incident Response
Security / Information Security / Information Assurance
Data Privacy / Data Security
Cloud Security / Solutions Architecture
Identity Management
Cybersecurity / Cyber Intelligence
Product Management
Service Delivery
Breach / Threat Detection
Previous Speaking & Attending Companies
Pfizer, Netflix, Deutsche Bank, CoreSite, FedEx, Credit Suisse, Evolutio, BNP Paribas, Wells Fargo, Cox Communications, Energy Transfer, Chevron, Morgan Stanley, Infiltron Software Suite, Ingenico, US Government, BMO, JMSI Vision, Leeds Building Society
BAE Systems, FIS, Barclays, SecurityHQ, McAfee, Nokia, Booz Allen Hamilton, Walt Disney, Boeing, Bestel, Bosch, Schneider Electric, Ericsson, Cognigo, Vesta Corporation, YETI, MUFG, Capital One, Telenet, Trustwave, Lockheed Martin
LinkedIn, Deloitte, Accenture, BBVA, Kiewit, Volvo, Visa, Raytheon Technologies, Hitachi, Lenovo, LG Electronics, EY, US Air Force, Preqin, Aerospike, Adobe, Fiserv, US DOJ, Duke Energy, Capgemini, PwC, Bitconnect, Universal Computer Center, Federal Reserve
Northrop Grumman, Huawei Technologies, Ball Corporation, General Motors, Symantec, Kaiser Permanente, Samsung Electronics, Panasonic, Hilton, Repsol, General Dynamics, Ingenico, Finastra, Bank of America, Union Pacific Railroad, Nomura, Refinitiv, and more!
Featured Presenters

Peter Wood
Partner
Naturally Cyber LLP

Eric A. Nielsen
CISSP, C|CISO, CCSP, HCISPP, CAP, CRISC, Chief Executive Officer
Defense in Depth Cyber Security

Natalie Timms
Security Operations Specialist
Cisco SECURE

Corey Kiesewetter
Sr. Product Marketing Manager
Forcepoint

Abdul Pasha
Director of Professional Services
Forcepoint

Erik Gibson
Team Lead, IT & Security
Konux

Jack Poller
Senior Analyst
ESG

Yotam Gutman
Director of Marketing
SentinelOne

Zain Malik
Senior Product Marketing Manager
Ping Identity

Lucy Yang
Principal
Identity Woman in Business

Kaliya Young
Founder & Principal
IdentityWoman in Business

Danna Bethlehem
Director IAM Product Management – Access Management and Authentication
Thales

Ryan Terry
Sr. Solutions Product Marketing Manager
Okta

Shane Moore
VP of Sales
Forcepoint

David Sherry
Chief Security Information Officer
Princeton University

Fazila Malik
Product Marketing Manager
StrongDM

Michael Wilson
Sr. Sales Engineer
StrongDM

Lance Malacara
Group Manager, Product Marketing
Okta
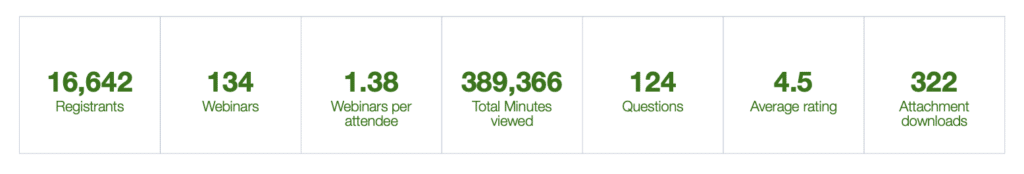
BrightTALK Cloud Security Summit Audience by Numbers (since 2019):